Enable IPv6 on a Secondary Router running OpenWRT
A guy with a keen interest in computer networks, software development, web technologies, embedded systems, and programming. When I am bored you can find me bingeing anime series, reading novels, and tinkering with hardware and software.
In recent years, ISPs here in Nepal have started deploying IPv6 in their network. For users who have a Linux server with tons of self-hosted things, this is a godsend feature. With IPv6 there is no need for NAT and any sort of complication. You just expose a port and make some firewall rules and you are ready to go.
In the case of Worldlink, it's the same. But the thing with Wordlink's CPEs is they haven't enabled any sort of firewall. This means all of the inbound and outbound traffic for the IPv6 is allowed. That means the devices have to protect themselves with their built-in firewalls. I am guessing they are doing this because they don't allow router access to the customers and users who want to add firewall rules for their IPv6 would have to contact them, which I am sure will be troublesome. So, they thought of letting it all in without thinking about the security consequences.
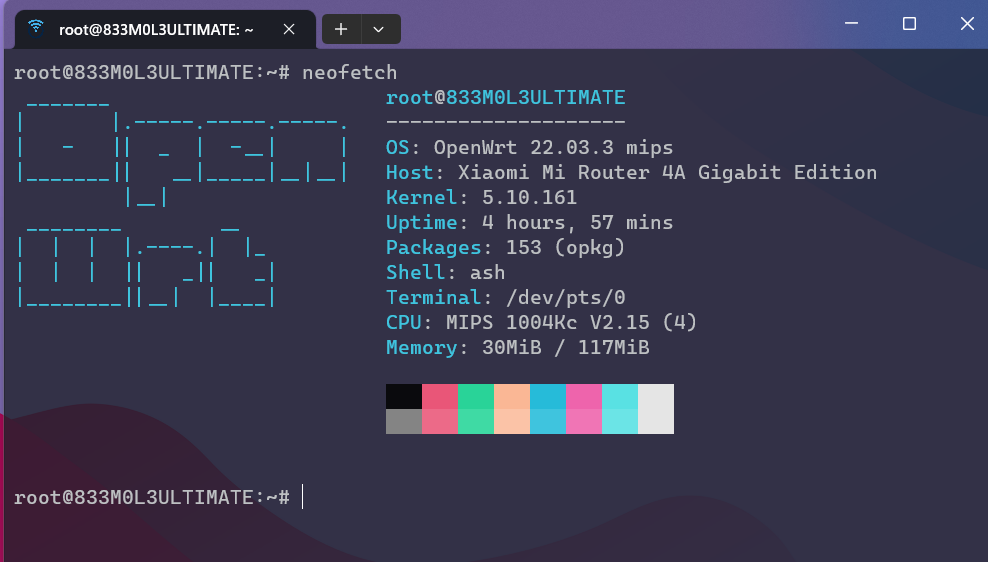
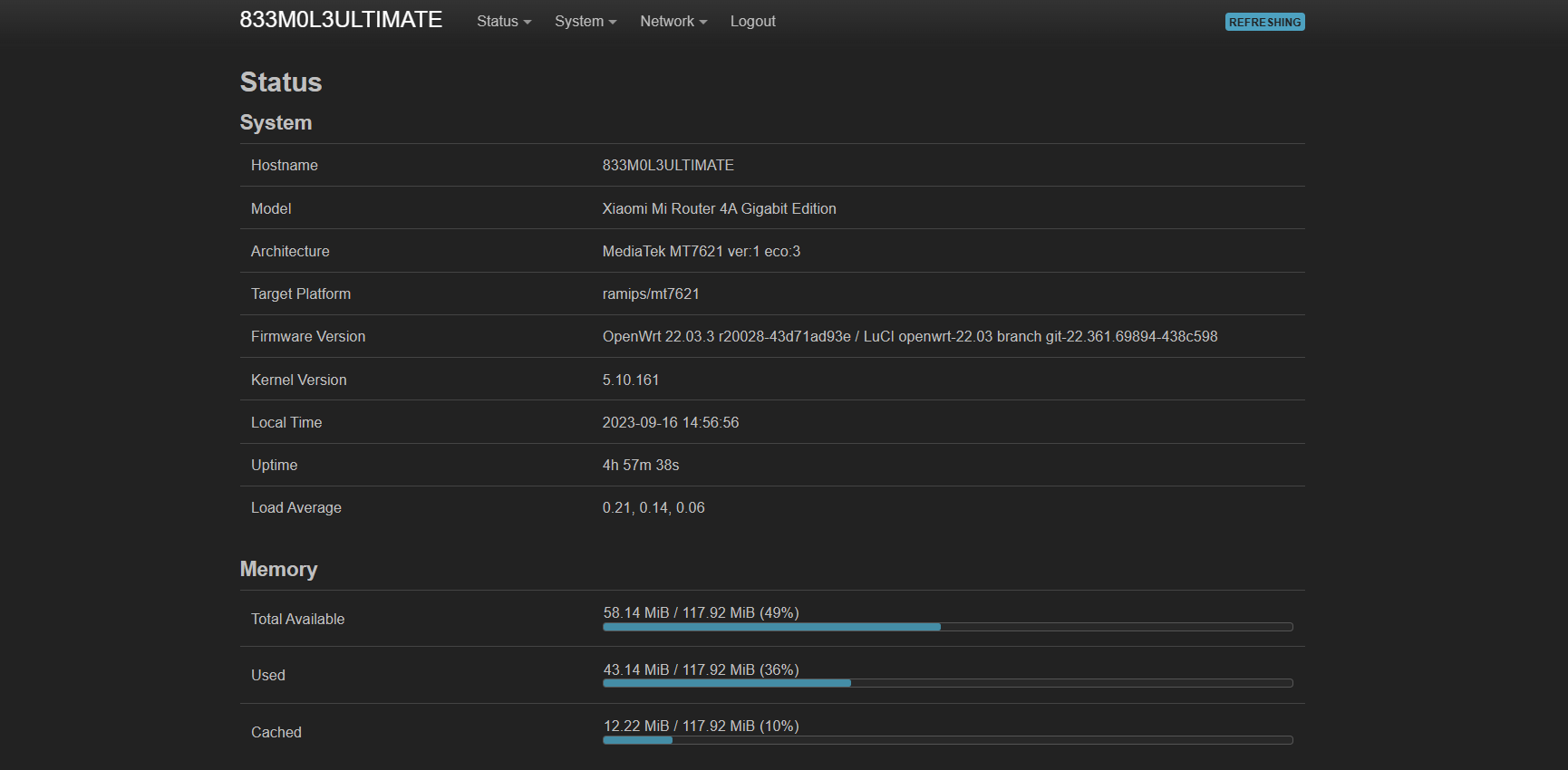
Too much restriction was also not my liking so I thought about getting a secondary router. I had a fair share of experience using and installing OpenWRT as previously I did a lot of experiments installing it on TP Link routers. But it was 2023, so I had to look in the market for some better routers with good support for the OpenWRT.
During my search, only one router popped up everywhere. It was Xiaomi's Mi Router 4A Gigabit. It had a decent processor, RAM was 128 MB and Flash Memory was 16 MB. What caught my eye was the RAM, that's really good.
So I bought one. Installed OpenWRT on it using this method, and got it running within a few minutes.
Now setting up the IPv6 was really a tricky part. Since my ISP provides a dual-stack IP, meaning I get IPv4 and IPv6 together. But the thing is, IPv4 is NAT and has no problem with me again putting it behind another network. But for IPv6 to work in such a way that every user connected to the Mi Router gets a public IPv6, the interface for IPv6 has to be set in a relay mode. Also, one of the reasons we are forced to use this relay mode or NDP proxy mode is because most ISPs in Nepal are assigning /64 address block to the CPE, meaning you can’t further prefix delegate the IPV6 to a larger pool. Though this current method does help with the IPV6 assignment via secondary router, without the prefix delegation, it is impossible to properly manage or create separate VLANs and networks.
To set the interface to the relay mode. Just go to the network interfaces.
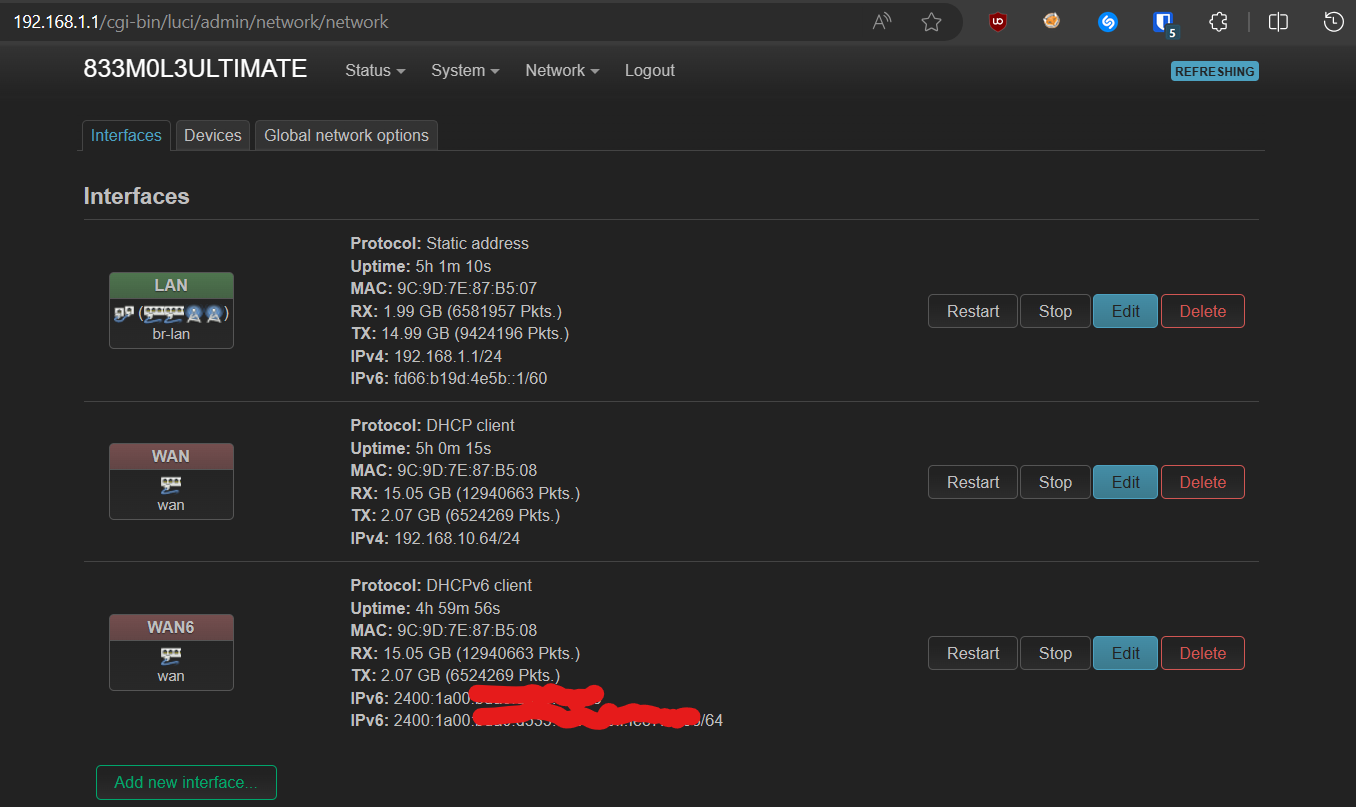
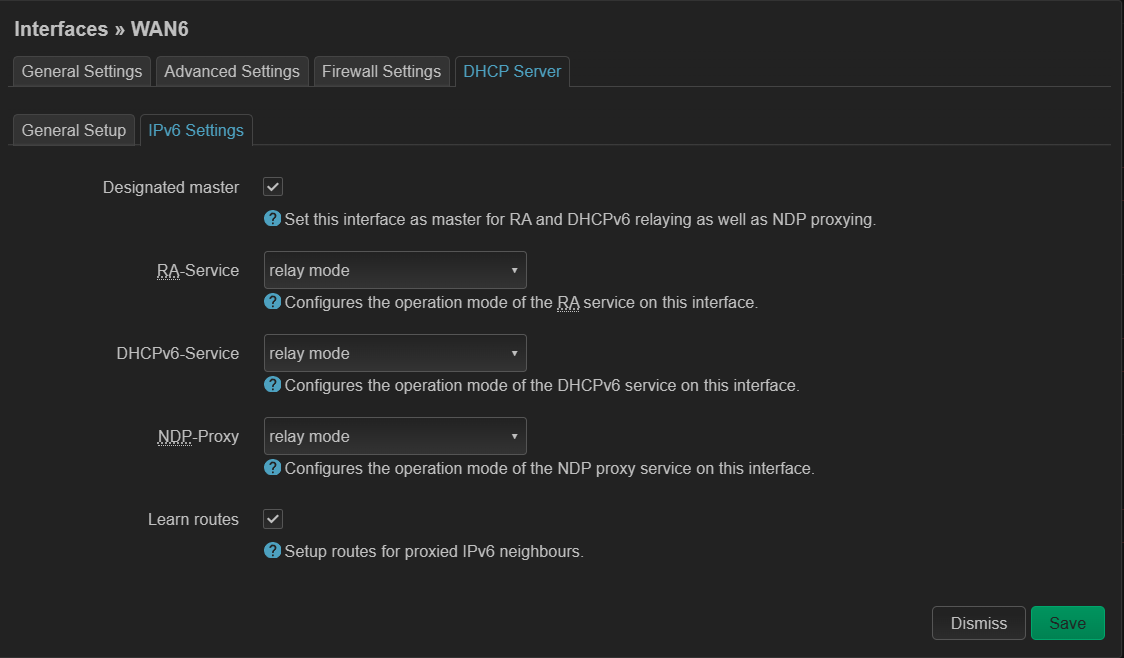
Edit your IPv6 WAN Interface and turn off the DHCP there. And make sure to change the IPv6 settings there as shown in the image below.
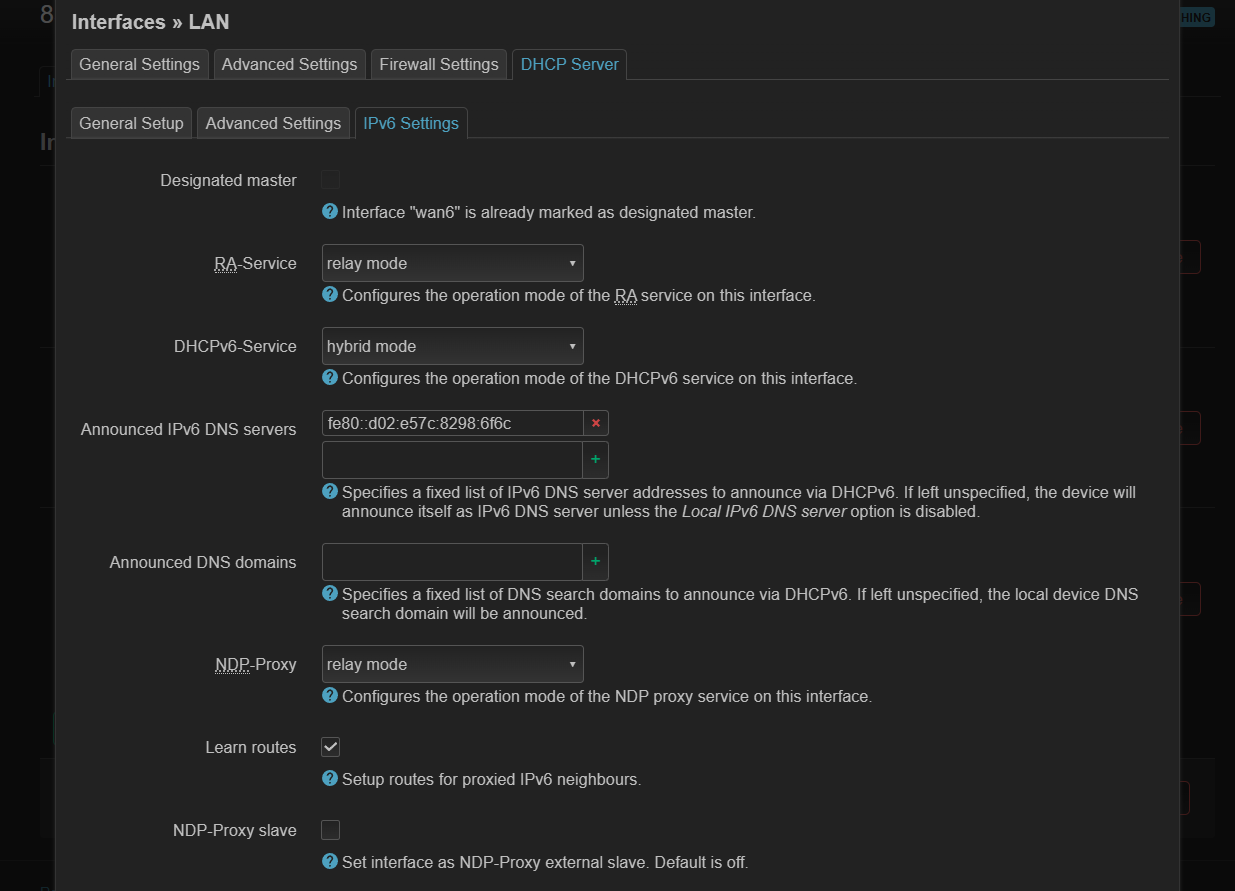
With that done, save it. And now head over to the LAN Interface. Edit the interface and go to it's DCHP Server Option and there make changes to the IPv6 settings as shown in the image below. You can skip the IPv6 DNS Server and leave it as it is.
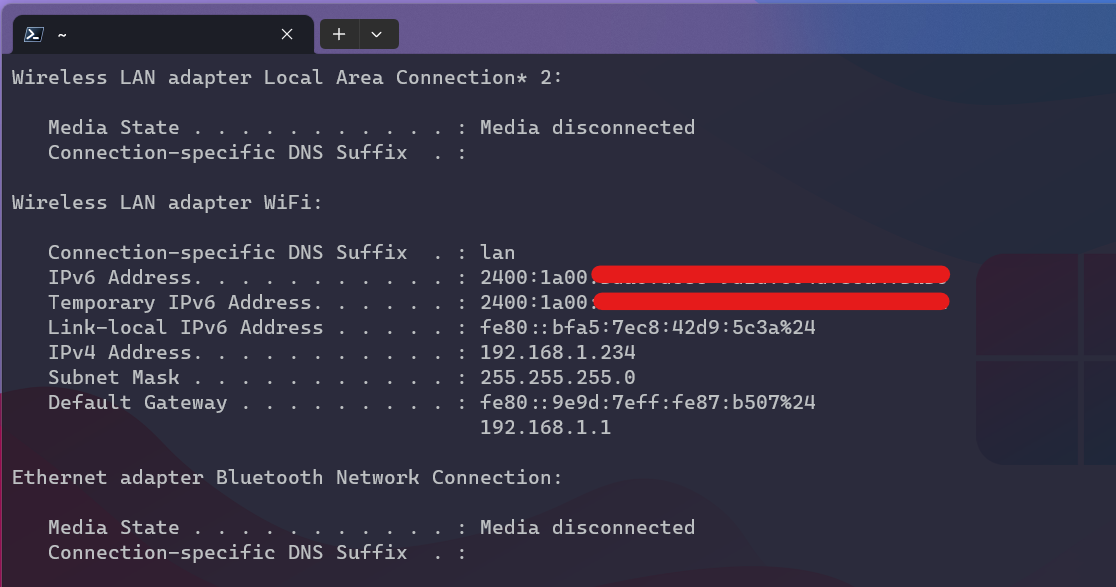
Now with that done. Save the changes and reboot your router. And you should start seeing your devices getting IPv6 assigned directly from the main CPE.
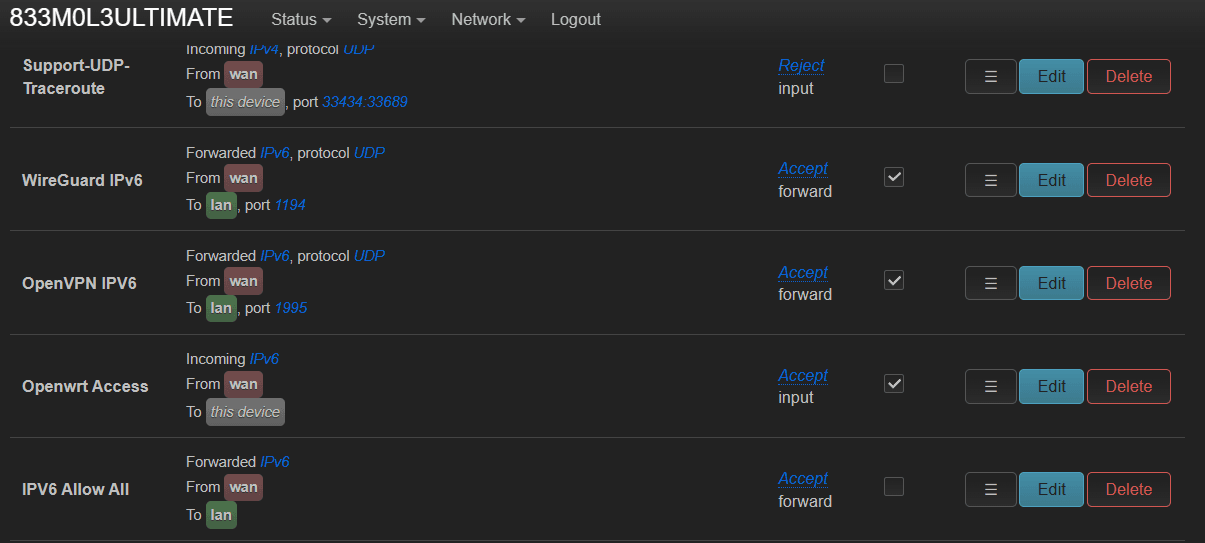
Now that's done. While exposing a port, you need to first allow that port from the firewall settings on your router. You can do that by heading over to the Firewall settings under the Network tab.
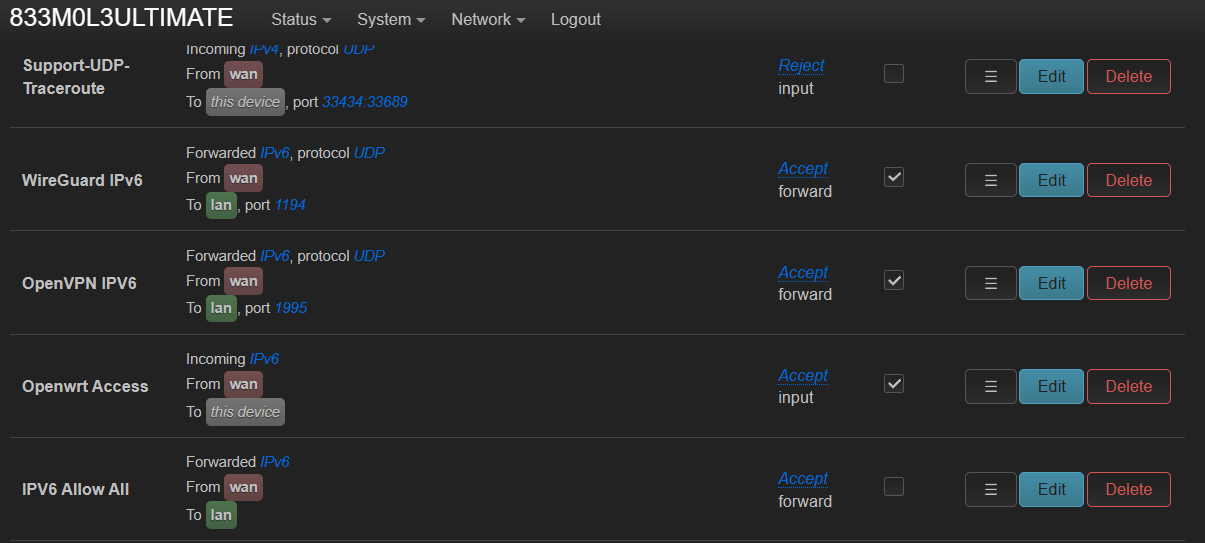
As you can see here, I have allowed the UDP protocol with ports 1195 and 1194. Those are for the VPN Server that I am hosting on my Linux servers. With that done those ports will be accessible by other IPv6 users.
Update 2025:
After the recent social media bans here in Nepal, many of us were forced to use DoH DNS services to bypass the blocks. And the best way to do that was to configure your router to do it. Normally, OpenWRT and most of the routers don’t come with DoH support; they only provide a plain IP input field to be sent to the DHCP devices. To fix this, you can self host a recursive DNS server and use tools like DNSCrypt to make those DNS queries go through secure DoH of popular DNS service providers like Cloudflare or Google. OpenWRT also provides packages that can forward your plain DNS requests to the DoH, which saves you the trouble of setting up the PiHole + DNSCrypt.
But the main issue is, when you are relaying the IPv6 to the devices, the router also automatically gives the default IPV6 based DNS servers that come with the ISPs. And it becomes really tedious to bypass.
Fortunately, you can change your IPV6 DHCP settings as shown below in the image to announce your own custom IPV6 DNS server even if it’s running in a relay mode. In the DHCPv6-Service set it to server mode and in theannounce IPV6 DNS servers, you will have to add your PiHole NAT6 local IPv6 address, or you could just input your OpenWRT’s default local IPV6 gateway there. Entering your OpenWRT’s default local IPV6 address will just forward it to whatever DNS server you have configured in your WRT’s router settings. Do note that this is a LAN interface we are configuring, not WAN6.
With that done, the devices will get two DNS assigned, IPV4 & IPV6 that you have set, thus bypassing the blocks.

You can see devices getting assigned the IPV6 DNS server you set in the Annouced IPV6 DNS Servers option.

I have PiHole + Dnscrypt setup, so it’s much easier to monitor and block domains that you don’t want. Though ISPs still can check your DNS Queries even if you use DoH or DoT. Using complex SSL inspection, they can check every packet’s SNI and implement a block based on that. So, using DNS over HTTPS is not a magical hack to bypass everything, but some ISPs do lack such hardware and software expertise, so if you are not a Worldlink user, then you are good to go.